
Shodan on Twitter: "Learn how to scan an IP or network using the Shodan command-line tool: http://t.co/gLAtKPpSVx http://t.co/3oocdBW0f3" / Twitter
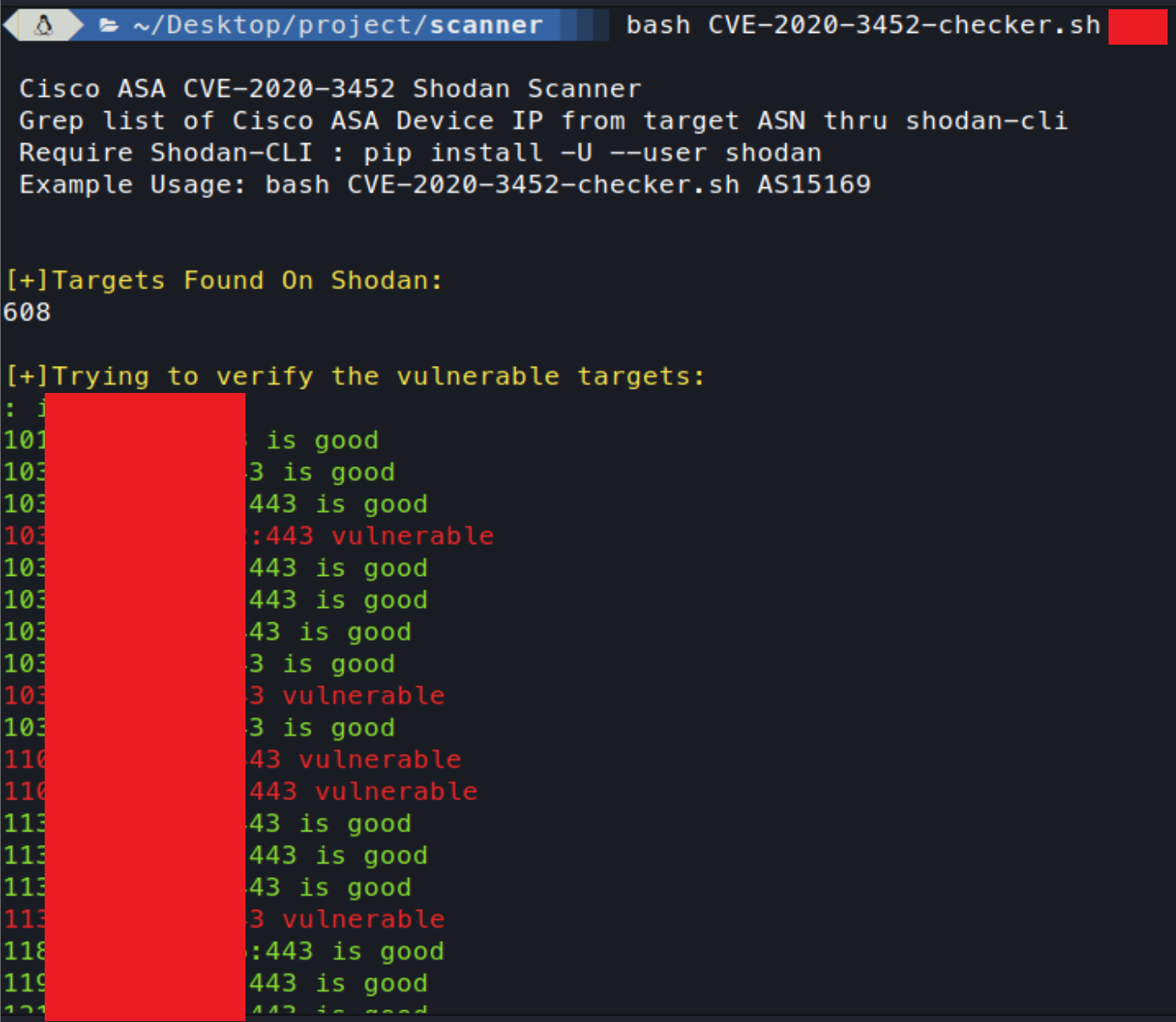
GitHub - faisalfs10x/Cisco-CVE-2020-3452-shodan-scanner: simple bash script of CVE-2020-3452 Cisco ASA / Firepower Read-Only Path Traversal Vulnerability checker

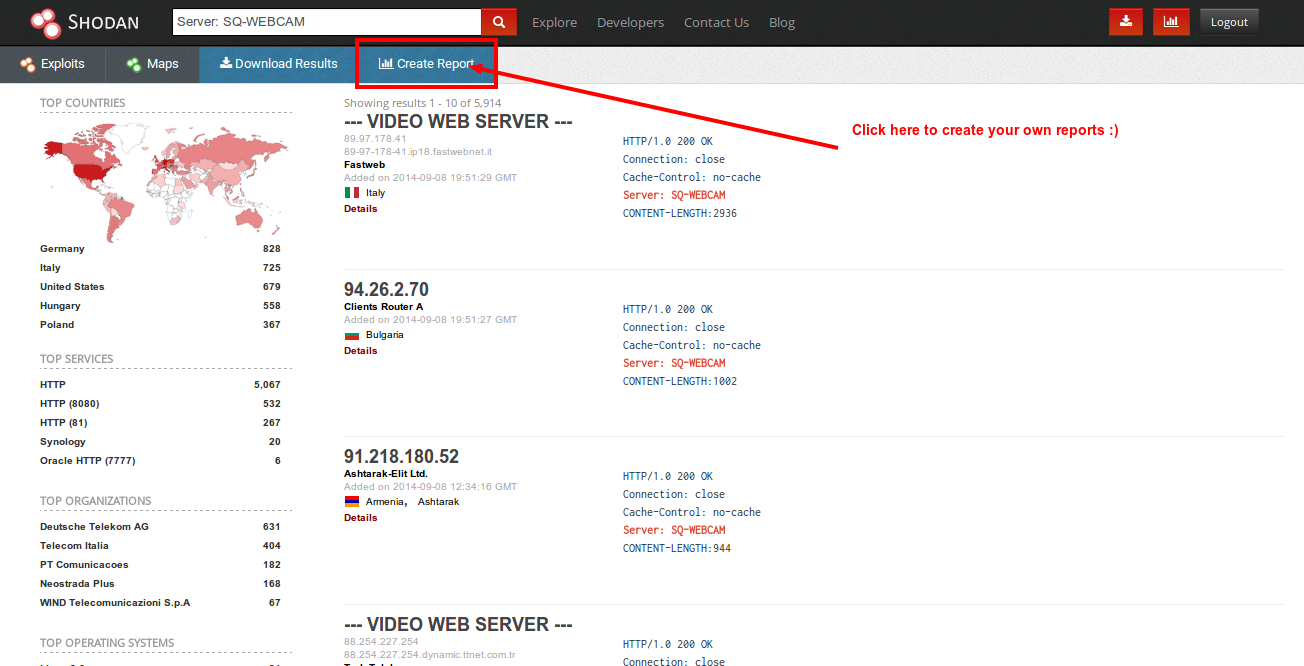
What are IoT search engines Shodan and Censys and what are they capable of | Kaspersky official blog

Shodan-based vulnerability assessment tool modular architecture. CPE,... | Download Scientific Diagram
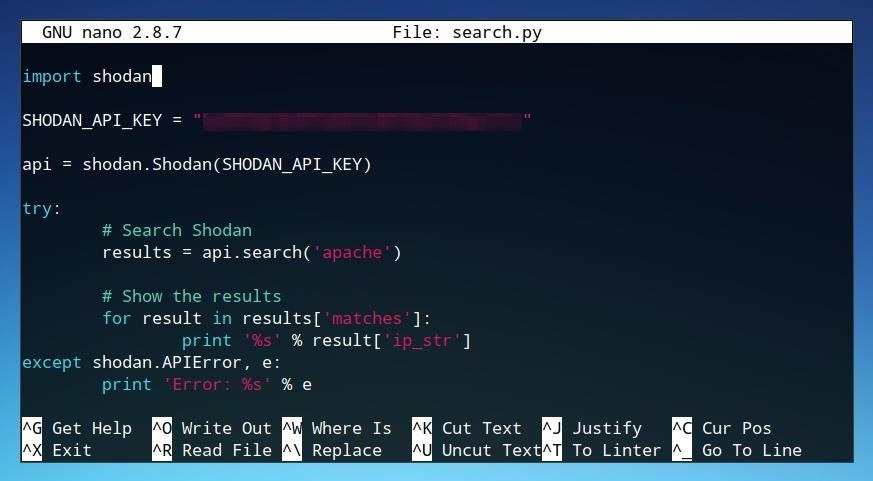
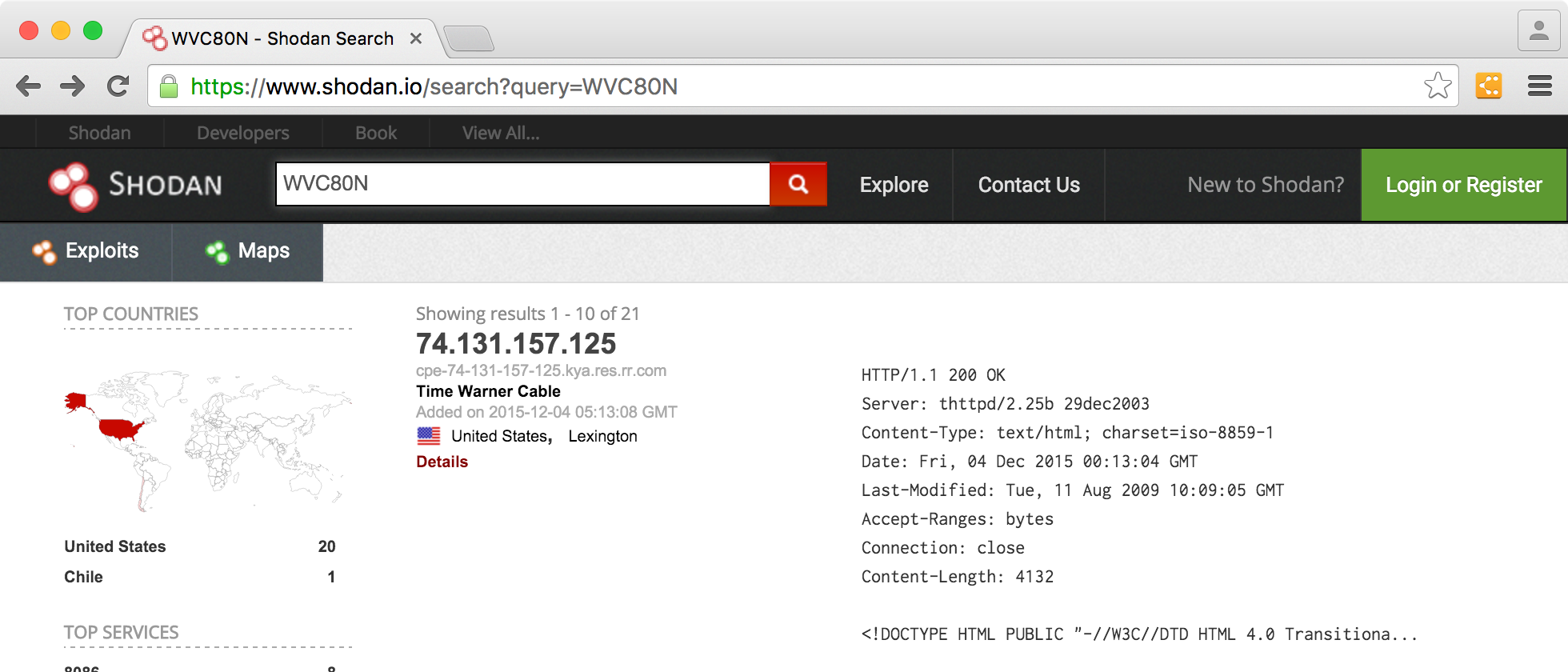
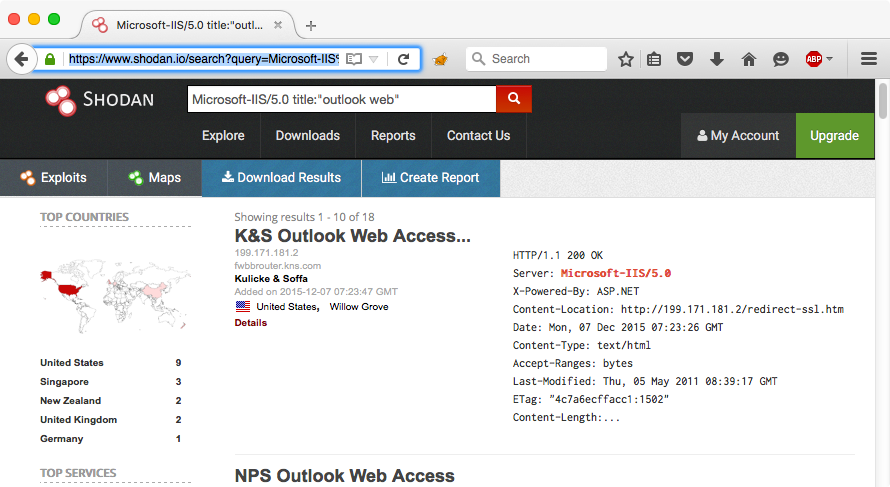
The Hacks of Mr. Robot: How to Use the Shodan API with Python to Automate Scans for Vulnerable Devices « Null Byte :: WonderHowTo

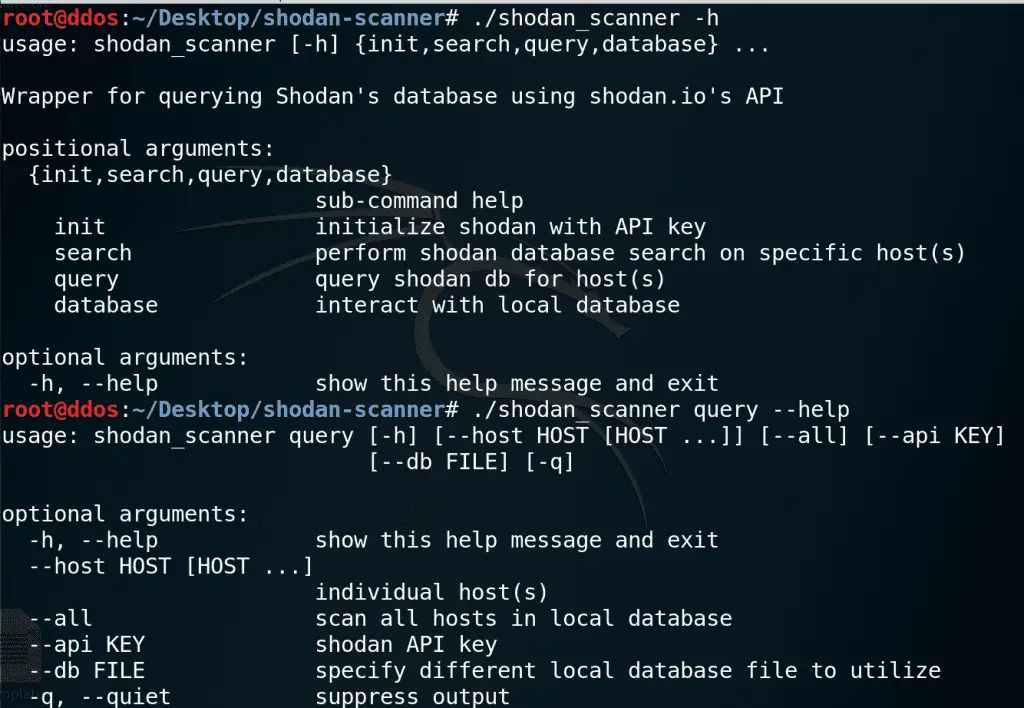
![Shodan Command Line a Step by Step Walkthrough - HackingPassion.com : root@HackingPassion.com-[~] Shodan Command Line a Step by Step Walkthrough - HackingPassion.com : root@HackingPassion.com-[~]](https://hackingpassion.com/shodan-command-line-a-step-by-step-walkthrough/featured-image.png)












![What Is Shodan? How to Use It & How to Stay Protected [2022] What Is Shodan? How to Use It & How to Stay Protected [2022]](https://static.safetydetectives.com/wp-content/uploads/2019/06/What-is-Shodan-and-how-to-use-it-Most_Effectively.jpg)